In 2016, krebsonsecurity.com was hit by a huge DDoS attack. Shortly thereafter, DNS provider Dyn went down, leaving many web applications unreachable. The Mirai malware drove the attacks by searching for devices with default credentials running telnet services, compromising them to create a botnet. In 2017, the Reaper malware created a botnet of IoT devices by exploiting a list of known vulnerabilities in web interfaces. Both malwares spread by probing random IP addresses, so only internet-reachable devices were potentially hackable and become part of the botnet.
Fortunately, most remote video cameras are not directly exposed to the internet. However, insecure cloud services put them at a similar risk of becoming part of the next IoT camera botnet.
Cloud protocols bypass firewalls and allow for connections into private networks.
This enables viewing remote devices that are in private home networks.
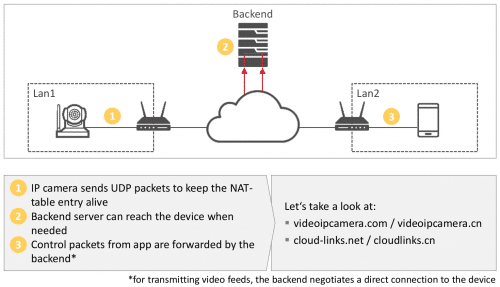
When an IP camera starts, it connects to the cloud backend and maintains the connection as long as the device is on. This enables convenient contact and control via a smartphone app from anywhere.
Two popular backends, videoipcamera.com / videoipcamera.cn and cloud-links.net / cloudlinks.cn have significant security issues at the time of this research in Nov 2017.
The backend can retrieve list of connected devices.
Device IDs have a length of up to six digits for Videoipcamera and up to seven digits for Cloudlinks. The validity of all device IDs can be checked unauthenticated within one hour via UDP. At the time of testing, there were 140,741 valid device IDs on Videoipcamera and 3,277,280 on Cloudlinks.
Certain types of packets are forwarded by the backend just based on the device ID. This allows for sending packets to all valid devices. A vulnerability in the handling of these packets would open up all devices to efficient exploitation. We did not find such an issue that would expose all devices to hacking, but several smaller issues that expose hundreds of thousands of devices, including the following issues.
Attackers can enumarate default and weak passwords.
By replaying packets with altered device IDs, it is possible to efficiently test passwords against all devices.
On Videoipcamera, 63,000+ devices (45%) are accessible via the default password 888888 and, based on a random sample, 700,000+ Cloudlinks devices are accessible with the password 123. A demo video is available.
Cloudlinks employs some rate limiting techniques that can be bypassed easily. Without factoring in weak user-choosen passwords, the cloud backends expose a total of 763,000+ devices with default credentials.
Remote exploitation automation.
To demonstrate the problem posed by this large number of accessible devices, we developed a remote exploit for Videoipcamera devices. First, the network settings are queried and the DNS server changed to redirect the device’s update requests. Then, a firmware update is initiated and a malicious firmware delivered. A demo video is available.
Creating a malicious firmware is relatively easy because the firmware relies solely on an MD5 checksum encrypted with a static DES key. Attackers can remotely execute commands on all Videoipcamera devices with known credentials.
Premium vendors share similar problems
Hikvision, the market leader, shares similar issues: Device IDs are not long enough to prevent enumeration. Our random sample of 100,000 IDs estimates 2,760,000 valid devices, with 50,000 using the default password ABCDEF after upgrading to cloud connectivity. Research by Jake Reynolds showed that the FLIR cloud service by Lorex, yet another vendor, allows direct tunneling across firewalls to arbitrary ports on the camera, just based on device ID. Subsequently, this allowed exploiting a known authentication bypass in the device’s web interface.
Network camera vendors need to improve the cloud service security.
The security of IP camera cloud services mainly relies on obfuscation through proprietary protocols. Large numbers of cloud-exposed devices in private networks will certainly capture the interest of bot herders, exposing users to privacy intrusions, and intrusions of their private networks; and exposing the internet to large-scale DDoS attacks. The internet should brace itself for ever-larger DDoS as insecure devices are unlikely to disappear anytime soon.
Research by: Balthasar Martin (@BalthasarMartin) & Fabian Bräunlein (@breakingsystems)
References.
Details were presented at DeepSec on Nov 16 2017: Announcement and slides.